Hill Cipher Program Source Code
Let’s learn how Hill Cipher works and everything you need to know about Hill Cipher with its implementation.
Code Issues Pull requests. Although there are different methods to encrypt and decrypt messages, we'll focus on a linear algebra-based cipher, the Hill cipher, which uses a matrix as a cipher to encode a message or an image, and it's extremely difficult to break when a large matrix is used. Cryptanalysis is the art of breaking codes and ciphers. When attempting to crack a Hill cipher, frequency analysis will be practically useless, especially as the size of the key block increases. For very long ciphertexts, frequency analysis may be useful when applied to bigrams (for a 2 by 2 hill cipher), but for short ciphertexts this will not.
When you are sending a text message to a friend, you don’t want your message to be manipulated or misused by an intruder. In order to avoid this, we need to convert the plain text data to a ciphertext. Before getting into this conversion let us first know what a ciphertext is.
Ciphertext
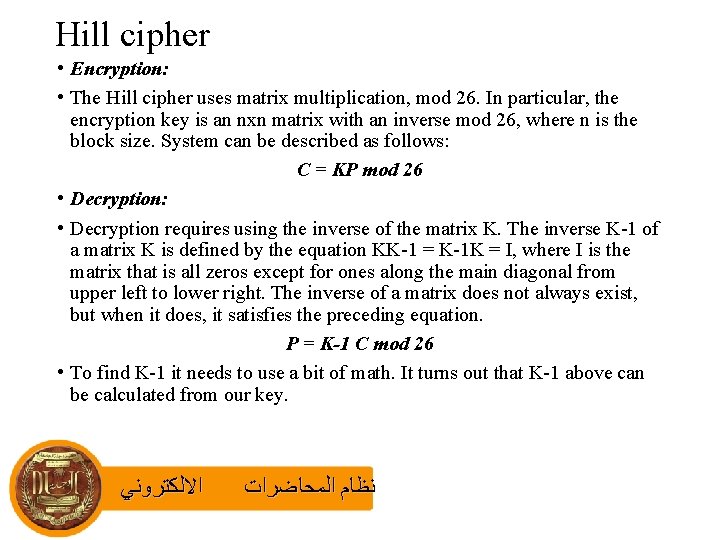
A ciphertext is a formatted text which is not understood by anyone. Hill cipher is one of the techniques to convert a plain text into ciphertext and vice versa. There are two parts in the Hill cipher – Encryption and Decryption.
Encryption – Plain text to Cipher text
Encryption is converting plain text into ciphertext. The working is shown below:
Input :
1.Plain text that has to be converted into ciphertext.
2.A KEY to encrypt the plain text
Output: Ciphertext
We have a simple formula for encryption
C = KPmod26
C is ciphertext, K is the key, P is the plain text vector.
Hill Cipher Program Source Code Example
The KEY is generally given in the problem statement. Here we are considering a 2×2 matrix. The plain text vector is represented as a column matrices that are considered one at a time. Since the key matrix is 2×2, we take each column matrix as 2×1. If the key matrix was 3×3, then each column matrix would be 3×1.
let us take an example where plain text is ‘exam‘ which has to be converted to ciphertext with key-value as now, form the column matrices into 2×1 configurations and covert the text into numeric data assigning values to each alphabet from 0 to 25.
a=0,b=1,c=2,d=3,………….,y=24,z=25
Consider the first column matrix and substitute in the above formula:
repeat this for second column matrix
Hence the final ciphertext is ‘elsc’
Decryption – Cipher text to plain text
Decryption is the conversion of ciphertext into plain text. It can be done by a simple formula
P=(K’)(C) mod26
where P is the plain text, K’ is the inverse key matrix, C is the ciphertext vector or the column matrices.
/arc-anglerfish-arc2-prod-mco.s3.amazonaws.com/public/62Y3T5JS4FCFXKQIZFDNKTSLUA.net635930348539146966)
Hill Cipher Program Source Code Download
Input: ciphertext and key
Output: plain text.
Here the C=’elsc’, which are further divided into column matrices: and K=
Now let us see the working:
1. First, find the adjacent matrix of the given key matrix
K_adj=
2. Find the determinant of the key matrix
77-88=-11
3. Find the modulo of the determinant with 26
-11 mod26 =15=d
4. Find the inverse number of the above result
d x d’=1 mod26
15 x d’=1 mod26
d’=7
5. Any negative numbers in K_adj should be added by 26 and then the whole matrix is multiplied by d’.
K’ =
Hill Cipher Program Source Codes
Now, this is our new key matrix. Substituting all the values in the decryption formula, we get the required plain text.
Repeat the above step using the other column matrix
Hence the final plain text is ‘exam’.
Hill Cipher in Java
Hill Cipher in Python
Also read: